Privacy Policies and Data Security Keep Contributions Flowing for Not-for-Profit Organizations
Dec 15, 2019
Steady streams of contributions are the lifeblood of not-for-profit organizations. Many factors that affect contributions are completely out of the nonprofit’s control – like changes in the economy and the budgets of the donors which may slow contributions to a trickle. However, one factor that isn’t out of the nonprofit’s control is a breach of privacy.
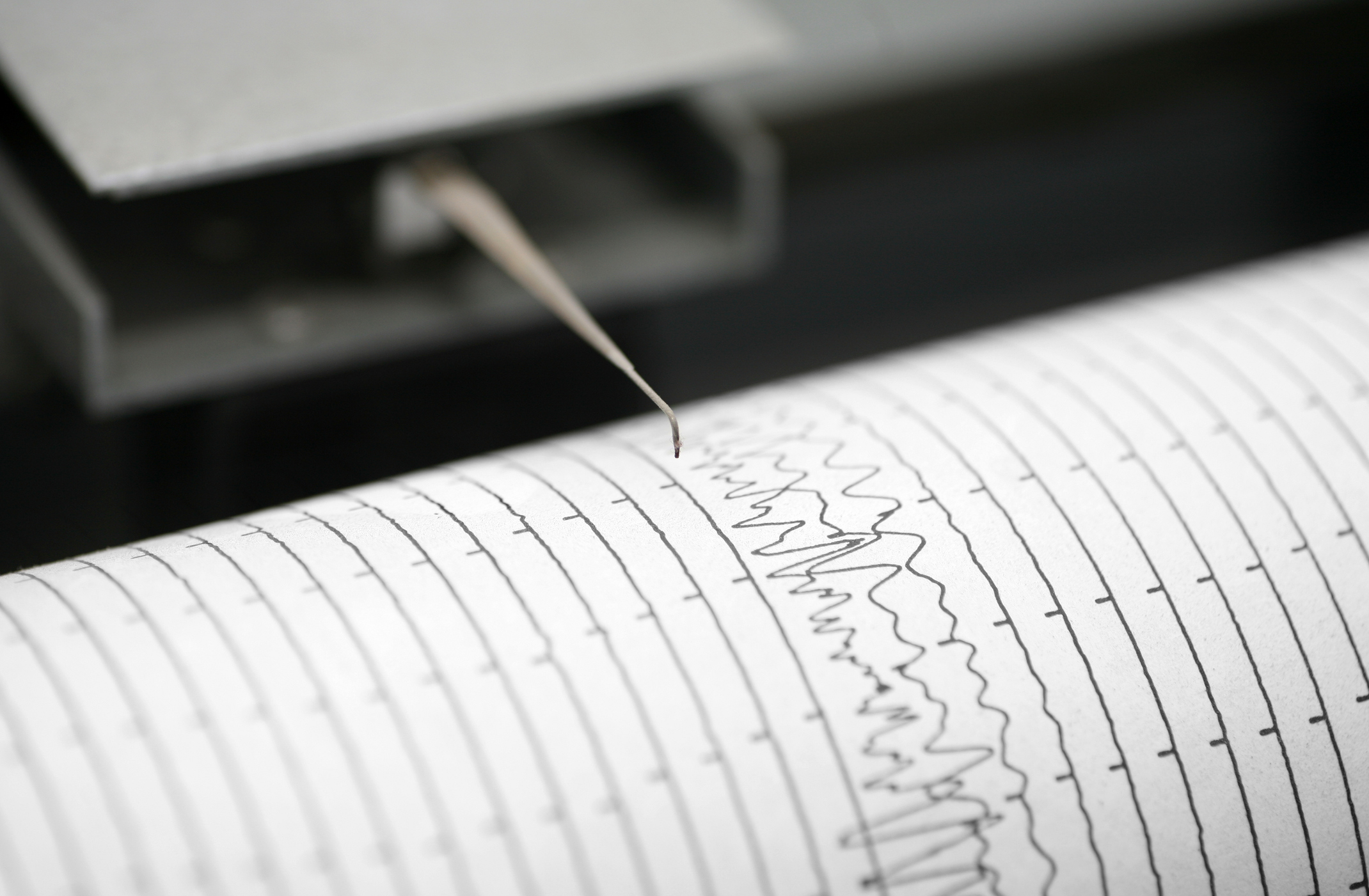
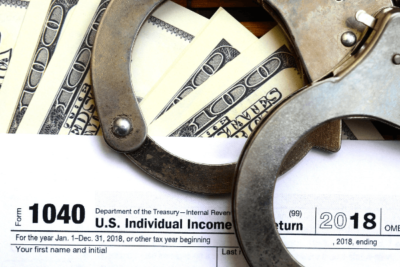
The Cost of Privacy Breaches
When a nonprofit has a breach of privacy, it may be through identity thieves who wish to use donor information to make purchases and obtain credit using a donor’s identity. Not only can this cost the donor money, but it can also result in hefty fines for the nonprofit that didn’t secure its system against breaches.
A breach may also occur when an individual or organization wants to obtain a list of donors in order to make it public, which could adversely impact the donors’ business and personal lives. The nonprofit could face resulting lawsuits and fines. There are some post-privacy-breach consequences that are more difficult to measure, such as the loss of an organization’s good reputation. Not only could the nonprofit lose existing donor contributions, but it may also have difficulty finding replacement donors.
Anonymous Donations
Donors to any cause should – and do – have the right to donate anonymously. For personal and professional reasons, there are donors who might not donate to a cause or organization at all unless they can do so anonymously. Anonymous donors expect their data to be protected from prying eyes. When a nonprofit doesn’t offer this protection, it risks losing money from lawsuits – as well as donors – and could even be putting its donors’ financial information and livelihoods at risk.
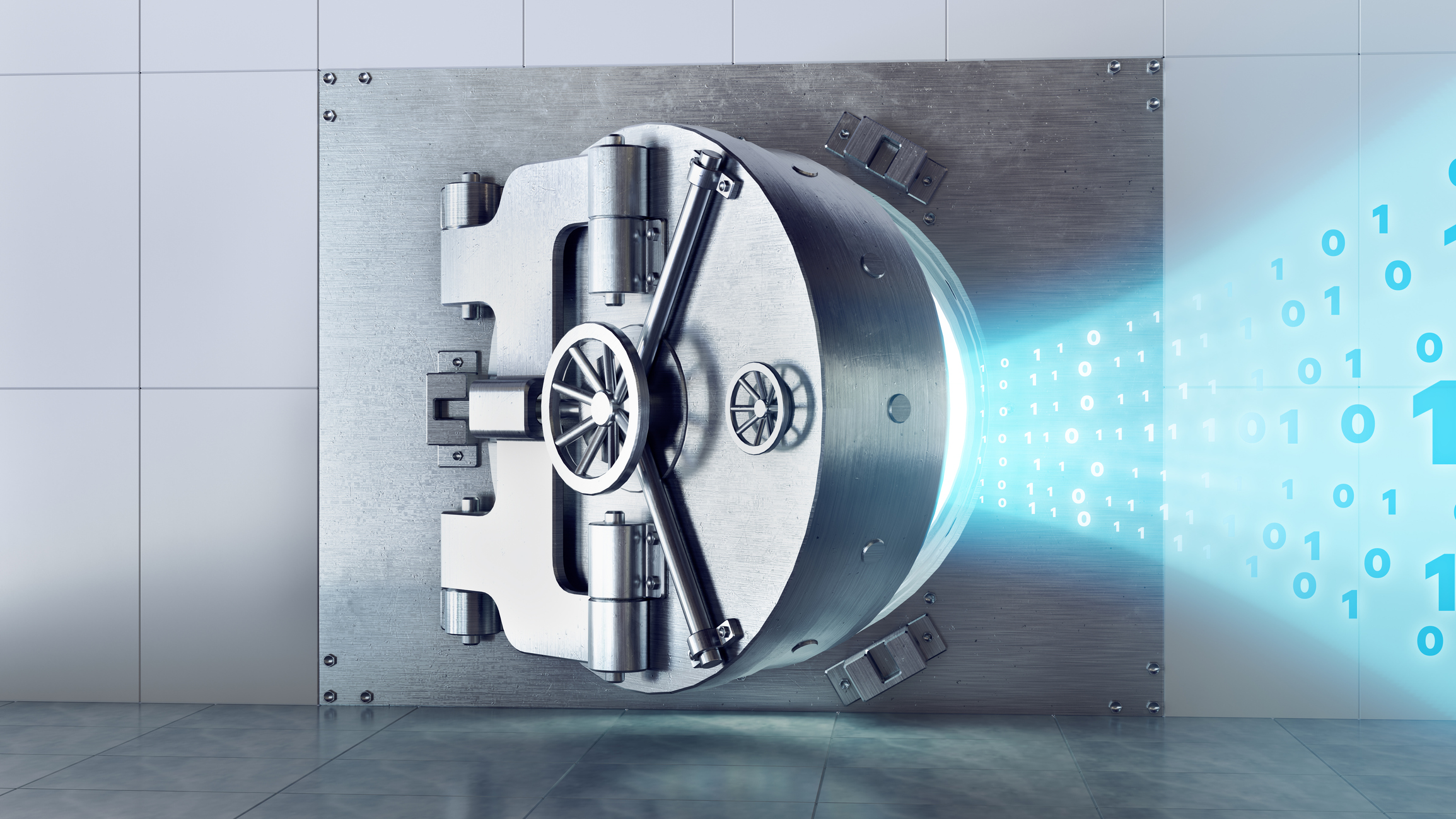
Preventing a Breach
Not-for-profit organizations can work to actively prevent data breaches and mitigate risk on multiple levels. Three initial steps include:
- Implement an effective password security system. It’s important that every member of the team who can access records uses a password. According to Microsoft.com, the ideal password should be original; consist of numbers, letters, symbols, and punctuation; and, ideally, be a nonsensical stream of at least eight characters, and the more characters the better. This password should also be changed regularly, and it should not be “daisy-chained” with any other system password. Daisy-chaining involves gaining access to a network or computer and using that information to gain access to other networks and computers using the same information.
- Create an employee policy for privacy and data security. Having all employees sign a nondisclosure agreement is the first step to ensuring that data is secure from hackers or a word-of-mouth breach. Create a system for handling confidential data in your employee manual. When clearly communicating the policy to all employees, explain the damages or repercussions of failure to comply. Then ensure that all employees are trained in its application and monitored in its use.
- Have an incident response plan for a potential breach. It’s not enough to work to prevent a data breach; develop an emergency plan for dealing with potential breaches. Managing reputation harm (including potential public relations issues), locking down data and networks, changing passwords, notifying donors, and utilizing the benefits of a cyber-risk insurance policy are components of a comprehensive emergency plan.
CRI’s cybersecurity team can help your nonprofit organization keep contributions flowing by reviewing your current controls and recommending solutions to properly secure donor data. Give us a call today.