How Does Your Industry Affect Your Cybersecurity Risk?
Feb 10, 2021
The consequences of a cybersecurity breach can be dire for any business, no matter your company’s size or the industry in which it operates. But your cybersecurity risk is driven largely by what you’re trying to protect — and those valuables are very much tied to your industry.
So: How is risk calculated, and what role does industry play in that formula?
A Calculated Look at Risk
Different industries have different frameworks for assessing risk. Banks can turn to the Cybersecurity Assessment Tool from the Federal Financial Institutions Examination Council. Healthcare providers and their business associates can conduct a HIPAA security risk assessment using the downloadable Security Risk Assessment Tool.
But at its core, cybersecurity risk boils down to a basic formula:
Likelihood of Occurrence × Impact of a Potential Breach ÷ Strength of Mitigating Controls
This seemingly simple formula requires quite a bit of nuanced understanding — of your business’s valuable assets and where they reside, of the weak points in your defenses, and of the best ways to lower your risk level.
Before examining the components of this formula, a note about inherent risk and residual risk. Inherent risk (represented by the numerator of the formula) is the “raw” level of risk that exists before applying any mitigating controls.
Residual risk is what you get by dividing your inherent risk score by the strength of your mitigating controls. Keep in mind that you don’t have to mitigate everything down to the ground. While you want your residual risk as low as possible, it will never get to zero. After all, there’s always a possibility of something completely unforeseen happening (hello, global pandemic!).
But if the likelihood of a breach is low, then inherent risk is probably also low. So rather than applying more mitigating controls that will have rapidly diminishing returns, shift your attention to the threats with a higher likelihood of occurrence.
Likelihood of Occurrence
Determining the likelihood of a threat boils down to two questions: What assets are we protecting? Are people motivated to steal them?
For a manufacturer, proprietary manufacturing processes and product launch plans might be attractive to competitors and even nation-state attackers. Companies that hold vast amounts of personally identifiable information (PII), such as healthcare and financial organizations, typically have a high likelihood of a breach by financially motivated attackers. Medical records, which contain all the personal details needed to pull off high-scale identify theft (e.g., date of birth, Social Security number, address, mother’s maiden name), are a treasure trove for malicious actors. Bank account, credit card, and debit card numbers, and even PayPal account credentials, are also valuable commodities on the Dark Web.
Impact of a Potential Breach
The second component of inherent risk is the potential impact of a successful breach. While there are nonfinancial factors to consider (e.g., reputation), ultimately, they all come back to the company’s bottom line.
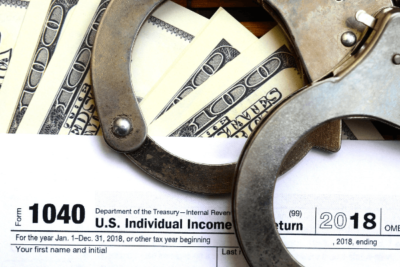
The cost of a data breach is closely tied to the type of data that is compromised. In IBM Security’s Cost of a Data Breach Report 2020, 80% of breached organizations said that customer PII was compromised, far more than any other type of data. Malicious attacks that resulted in customer PII being lost or stolen were the most expensive, with an average cost of $175 per record.
The cost of a data breach varies widely by industry. Healthcare organizations consistently incur the highest cost per data breach. In the 2020 IBM study, healthcare organizations reported an average $7.13 million cost per data breach — nearly double the $3.86 million average across all industries. The energy sector had the second-highest price tag ($6.39 million), and the financial industry ranked third ($5.85 million).
What do these industries have in common? Regulatory scrutiny. “Organizations subject to more rigorous regulatory requirements had higher average data breach costs,” the IBM report states. But the cost of compliance isn’t the sole factor that makes breaches in regulated industries so expensive (although those fines can certainly pack a punch). At the end of the day, lost business is just as damaging as regulatory fines. In the 2020 IBM Security study, lost business costs (customers who defected because of the breach, increased cost of acquiring new customers due to diminished goodwill, revenue losses from system downtime and business disruption) accounted for nearly 40% of the average total cost of a data breach, more than any other cost factor.
Mitigating Controls
One way to assess the state of your company’s mitigating controls is to ask, How quickly can we catch a breach? On average, companies in the IBM Security study required 280 days to identify and contain a breach, but the breach life cycle varied widely depending on the industry. In healthcare, the life cycle averaged 329 days — which was 96 days longer than the average in the financial sector. The adoption of security automation sped up the average time to identify and respond to a breach, reducing the average life cycle of a breach by 74 days.
Also ask, Are we doing all we can to protect our valuable data? And if so, is that enough? Maybe you have invested all the resources that you can in automated controls, but the risk still isn’t mitigated to an acceptable level. Could you institute a process whereby manual inspections supplement automated controls? In cases where the residual risk remains too high, companies increasingly transfer this risk using cyber insurance. In the IBM Security study, 51% of respondents had submitted cyber insurance claims to cover the cost of consulting and legal services.
What’s Your Risk Factor?
On a personal level, you probably don’t think about risk in a particularly formulaic way. You likely have a gut-level understanding of how risky different scenarios are. But when it comes to your business, you can’t afford to rely on a gut check. Even if you think you have a good handle on your company’s valuable assets and the potential holes in your defenses, without a documented cybersecurity risk assessment, you’re probably missing something.
The most important factor in assessing risk is the value of what you’re trying to protect — both to your organization and to potential attackers. Contact your CRI cybersecurity specialists to discuss how you can put in place a strong cybersecurity risk management program that is rooted in knowledge of what your data is worth.